ConfigCat’s Security Framework
Nowadays, almost each and every business uses some sort of web application, so cyberattacks are becoming a daily struggle for huge enterprises as well as for small businesses. It’s not enough for programmers to build an application that looks great and works smoothly. Many consumers are getting aware of the need for security in the applications they are using.
As ConfigCat is a Software as a Service business with applications running in the cloud, we take security as seriously as reliability. Here are the security measures we take to ensure that we deliver a secure application.

Software development security
The application layer is the hardest to defend, and this is also the most accessible and most exposed to the outside world. By adopting security precautions and carefully reviewing code, the likelihood of successful attacks can easily be eliminated. Let’s see how we make sure that we protect the application layer of ConfigCat.
Security culture
The development process of ConfigCat is based on the Microsoft SDL (Secure Development Lifecycle) principles. This means that our developers have up-to-date knowledge of the latest security notions and use them effectively while building our backend and frontend. As part of the lifecycle followed by ConfigCat, we review our code every quarter based on the guidelines of OWASP Top 10 Most Critical Web Application Security Risks.
Security testing
Unfortunately, every single complex software has vulnerabilities. Also, every complex software uses components that haven’t been written by you or your team members. Such components can come from either third-party vendors, or they can be open source projects hosted on development platforms such as GitHub.
Static Application Security Testing
For static security testing (aka testing your application by analyzing the source code or binaries without execution), ConfigCat uses SonarQube as a Static Application Security Testing (SAST) tool. Using SonarQube for static analysis is an essential part of our development lifecycle as it provides immediate feedback to us on security flaws we might be adding into the code during code development itself. We use this tool to detect vulnerabilities, understand their nature, and get appropriate next steps.
Software Composition Analysis
ConfigCat uses open source libraries as dependencies in the SDKs, but we make sure that those components are free from any vulnerabilities by using a software composition analysis tool like Snyk. This tool helps in our development process to ensure that we use the latest version of every component. The usage of Snyk is essential because ConfigCat SDKs are open source, giving full transparency over the quality and security of code you will add to your application.
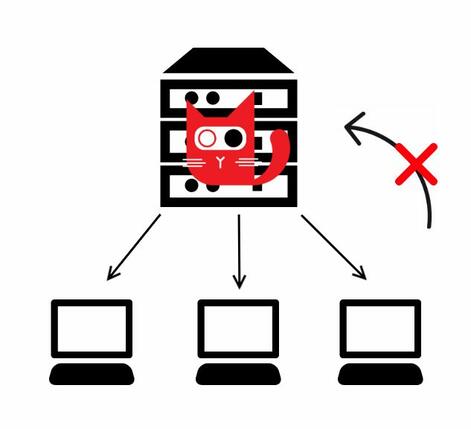
Privacy by Design & Data minimization
ConfigCat’s architecture is designed so that the feature flag evaluation is on the client-side within the ConfigCat SDK. This ensures that our customers’ data never leaves their system. We only store feature flag details like name, key, description, value, targeting rules, and percentage rules. You can read more about ConfigCat's architecture here.
Security features
We make sure that all the security features we provide are included in all the subscription plans; therefore those who opt for a free subscription can also access these features.
Authentication & Authorization
Simply put, authentication refers to the process of determining someone’s identity, while authorization means what permissions someone has to specific resources.
Single sign-on (SSO)
For more secure and simpler access to the management console, ConfigCat provides Single sign-on (SSO) authentication. Using SSO increases security and there is less risk of accounts being compromised.
Read more about ConfigCat’s SSO authentication.
Two-factor authentication
You can easily add an extra layer of protection to your ConfigCat account by enabling two-factor authentication. Under “My Account”, go to “Enable two-factor authentication” and scan the given QR code on your Windows, Android or iOS device. You can use any type of authenticator app you prefer (e.g. Onelogin, Microsoft, Google, etc.).
Role-based access control (RBAC)
Role-based access control (RBAC) is offered on the ConfigCat Dashboard and allows our customers to define roles and permissions for their team members to make sure no one turns an incomplete feature on in production by accident. You can read more about permission groups here.
OAuth2 protocol for authorization
A simple and effective way to provide explicit authorization flows for web applications and APIs is through an authorization server. The ConfigCat Dashboard web application and the linking REST API use OAuth2 protocol for authorization.
Feature flag values are behind an SDK Key
You can only access your flags using different SDK keys for each of your environments. Plus, we provide SDK key rotation so our subscribers can change their SDK keys gradually and independently without any business interruptions.
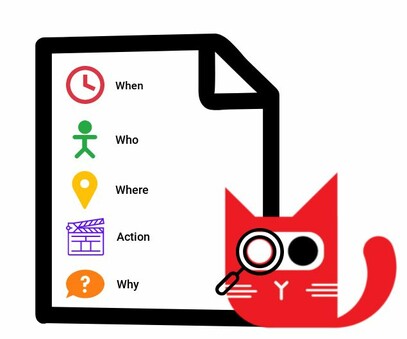
Audit trail
There’s no secure application without detailed and continuous audit logs. Proper logging provides accountability by providing enough details and context to answer the who did what and when questions. At ConfigCat, an audit trail shows a complete record of actions and changes that take place with a feature flag. Audit logs are also essential from a compliance perspective. For instance, a ConfigCat customer requested “Why” column to be added to our audit logs to comply with their SOC2 requirements so now if you decide to switch the “Why” column on in the ConfigCat Dashboard, it’s mandatory to explain why you’ve changed any of your feature flags’ value.
Cloud infrastructure and data centers
All of our services run in the cloud and are located within the EU to comply with GDPR. Our services rely on Microsoft Azure, Digital Ocean, and Linode cloud providers. They provide security measures to protect our infrastructure and are compliant with most certifications. You can read more about their security practices here:
- Linode: https://www.linode.com/legal-security
- DigitalOcean: https://www.digitalocean.com/legal
- Microsoft Azure: https://www.microsoft.com/en-us/security

